Audit Log Process Changes in SAP Ariba
If you encounter an error message in your SAP Ariba audit log beginning Oct. 1, 2023, this is the reason why. Starting then, all new audit data will be written to the SAP Ariba audit service.
What is Changing?
Beginning October 1, 2023, all new audit data in SAP Ariba will be written to the SAP Ariba audit service and no longer written to the legacy audit logs. You may have seen this warning as you accessed the legacy means of exporting audit data in your site:
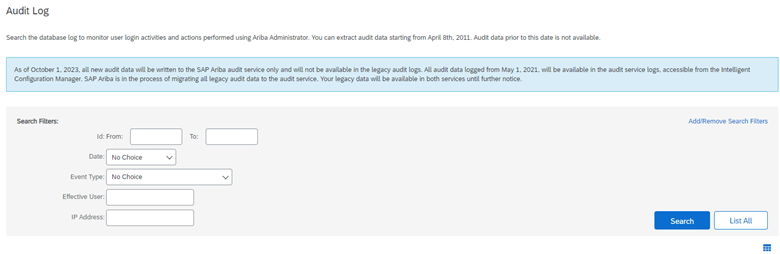
Currently, you can access your audit data by clicking on “Audit Log” under the Site Manager section of Core Administration, searching as needed, and use the typical “export all rows” processes. However, starting in October, you will need to find your audit information in the Intelligent Configuration Manager tool by clicking “Configurations” in the Intelligent Configuration Manager section of Core Administration.
Audit Info moving to Configurations

Two Important Changes
Although the notification banner only alludes to a change in location, there are two significant changes that SAP Ariba administrative users need to be aware of:
1. The “Event Type” dropdown values have changed significantly.
They no longer match 1:1 with the legacy audit event type values. SAP Ariba resources have assured us that a mapping file/data dictionary is forthcoming to help users know what to select going forward based on their legacy selections, however that has not been provided yet. For example, during our testing, we have found most of the data previously held under the legacy “Admin (tasks/files)” to be available in the new event types of “Security”, “Generic Action”, “Configuration Modification”, “Data Modification”, and “Integration”.
Until SAP Ariba’s mapping document/data dictionary is published, current admin users will want to set aside time to thoroughly explore the data associated with the new event types to make sure they are aware of where to get the necessary information for their audit activities.
2. Exporting data has become more secure, however it requires more technical ability and extra steps to do manually.
In order to comply with generally accepted industry standards, enable an Audit Search API, and to protect sensitive audit data, the new ICM-based Audit Logs will require the use of OpenSSL public and private key pairings to encrypt the report data to be downloaded and decrypt the resulting .zip file.

For those customers with a solid grasp of public and private key pairings, use of terminals and command lines, this may be a non-issue. However, for those users with a more functional focus, some acclimation with these tools will be necessary in order to manually export your data for use outside of the user interface.
Windows end users will need to install some sort of Unix command line terminal along with the necessary packages to manually encrypt/export/decrypt their data. Ariba recommends the tool CYGWIN and includes some basic information about what is necessary, including the Unix packages necessary to enable during the installation (openssh, unzip, unzip-debuginfo). As such, users in restrictive IT environments may want to work with their IT departments for the necessary permissions to have this tool installed on your computer.
If you are regularly exporting audit information in the course of your duties, plan on an additional 15 minutes of setup and then an additional 3-7 minutes of decryption work PER EXPORT, depending on your level of comfort working in a command line terminal. Please note per item 1 above, you may need to do more than one export in order to retrieve all the data necessary for your audit processes.
Need Help?
CCP Global has worked through this encryption/decryption process from the perspective of a functional admin user, including the installation of CYGWIN and can assist you with this change.

